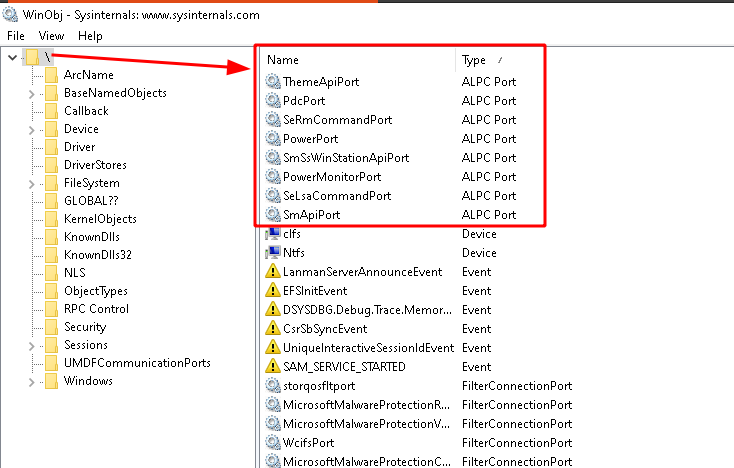
Alex Ionescu on Twitter: "@lordx64 @stvemillertime It's “\Windows\ApiPort” an ALPC port owned business CSRSS. Since NT strings are not null-terminated, you're seeing the reuse of a buffer that contains “SharedSection”." / Twitter

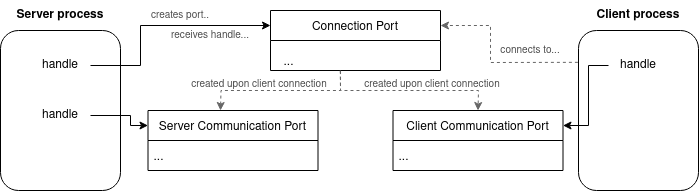
alpc-rpc.pdf - A view into ALPC-RPC Introduction ALPC RPC UAC Advanced features & vulnerability research CVE-2017-11783 Conclusion A view into | Course Hero




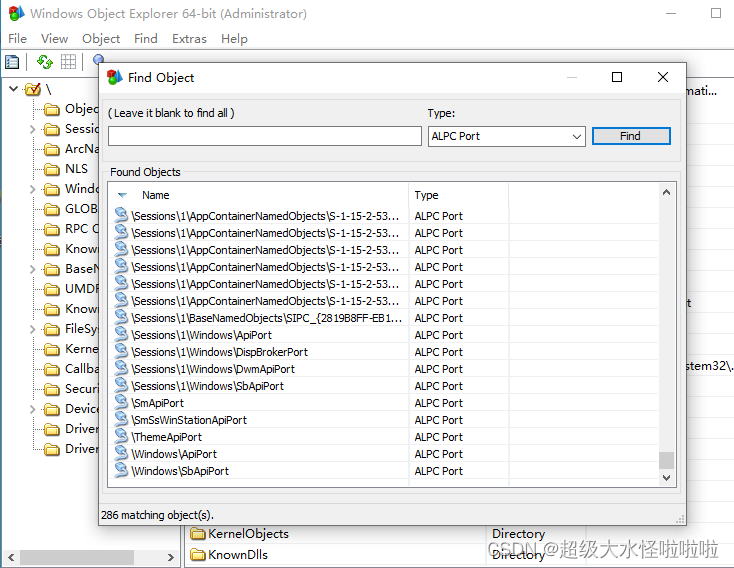
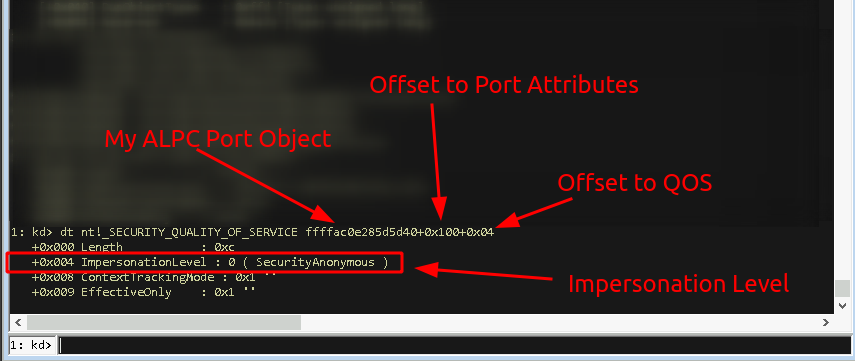
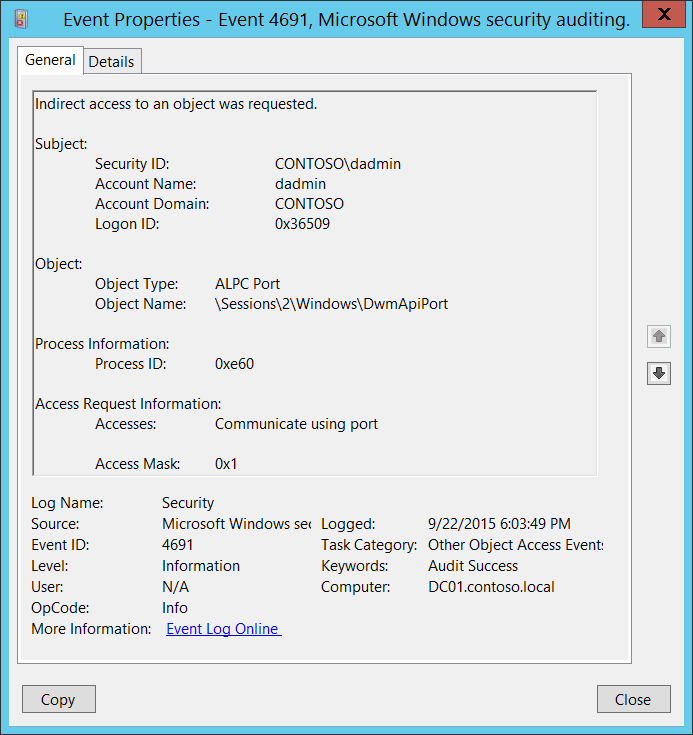
![原创]Windows不太常见的进程注入学习小记(二)-编程技术-看雪论坛-安全社区|安全招聘|bbs.pediy.com 原创]Windows不太常见的进程注入学习小记(二)-编程技术-看雪论坛-安全社区|安全招聘|bbs.pediy.com](https://bbs.kanxue.com/upload/attach/202008/795949_88QEJMQ8WMG87X3.png)